A Look At The Cutwail Botnet Malware Campaign
By David Cawley | 3 minute read
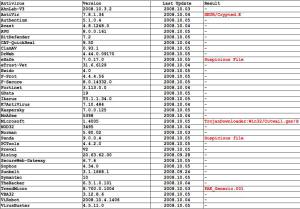
virustotal which is an excellent resource for classifying suspicious files and showing the definition coverage from various companies. Here’s a screen shot showing the coverage.
So, what does it do? The file attached to the e-mail is Statement_1.zip and it contains a malicious file named Statement_1.doc.exe. Running it in a sandbox environment, shows that it copies itself to a file named rs32net.exe and then adds it to the registry so it will be automatically run on system startup. It also sends a http GET request to 208.66.194.240, 208.66.195.71 and 216.195.55.50 on port 80 to download additional files and to register itself as a new bot with command and control. It then attempts to connect to mailservers to verify it can send before attempting to send on the same message with the malware payload.
The current campaign spreading the malware, tries to convince the recipient that they have been a victim of credit card fraud and the statement with fraudulent transactions have been attached. Here’s a sample e-mail and Subject lines being used include “Security Department”, “Credit Card Fraud Involving”, “Fraud Transactions”, “Fraud Defense”, “Dear Holder”, “Information of Your Transactions” and “You the Account Statement”.
Greating and salutations
Dear Credit Card Holder:Please be aware that a credit card fraud involving your credit card
has been registered by our security department. For your information,
we are sending you the account statement that includes all transactions
made with your credit card from 01.09.2008 through 03.09.2008.
Please take a note of the last three transactions on the list,
which have been recognized as fraudulent.We highly recommend you to inform us of the transactions you have
made personally. Thus, you will help us and yourself to resolve this issue
as soon as possible.An MS Word document containing your account statement in is enclosed
in the archive attached to this message.Take care of yourself
Selma Rosenberg
Manager of Credit Card Fraud Defense
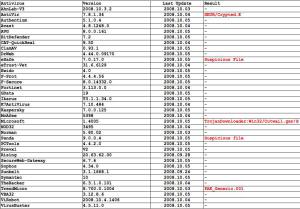
Update: On Tuesday morning I noticed a change to the malware being delivered. The latest Trojan downloader was not identified by most major AV solutions and it behaved differently. It downloaded the files loader.exe and install.exe from soft-side.net and mncpssa.org. It also attempted to check a block of IP addresses of a corporation on port 445.
Update 2: On Wednesday morning around 5am, the attached Trojan was changed again. Only 3 AV solutions identified it but with general names e.g. “Suspicious File”, “Suspected of Malware” and “New Malware.ix”. I wonder if it will change again tomorrow?